CryptoWall
A variant of the Cryptorbit or Cryptolocker ransomeware called CryptoWall is doing the rounds.
For those of it who are not familiar this is a very clever scam where you are sent an attachment that has an encryption process embedded in it.
The malware trawls your PC and all mapped network drives for useful files such as images, documents, text files, excel, database files and encrypts them. It is very fast as it only encrypts a tiny proportion of the file and then renames it to random text and extensions.
Source
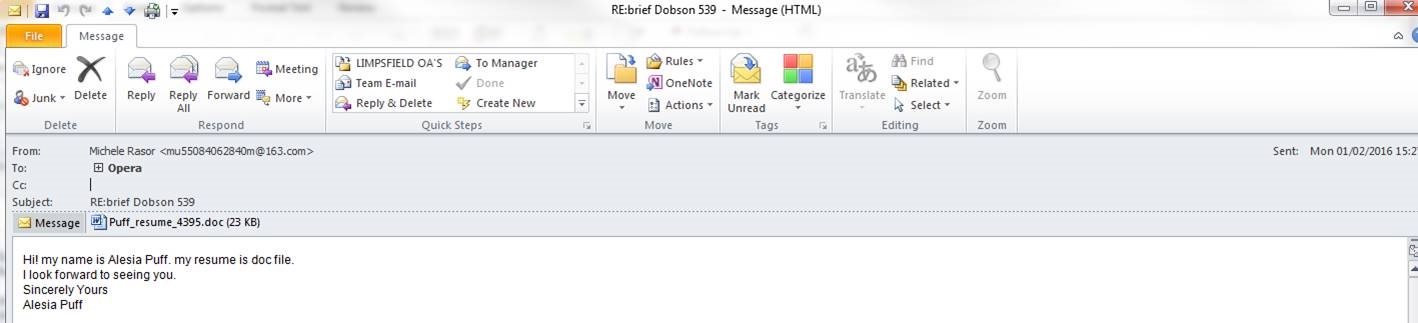
This is one variation of the sort of e-mail you may receive and it may appear to be from someone you know. Pay attention to the From: field and the e-mail address. This will usually be the give-away. Plus the text in the e-mail is brief and usually strange or irrelevant.
NEVER OPEN ATTACHMENTS UNLESS YOU ARE SURE THE SENDER IS LEGITIMATE.
 Watch out!
Watch out!
Before you know it, files on your PC and network drives will become encrypted and renamed.
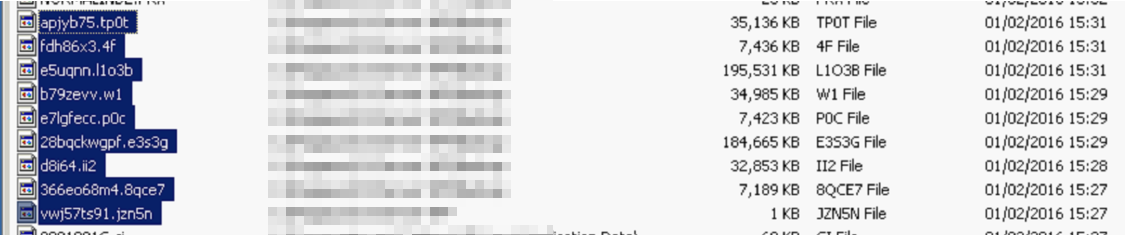 Encrypted Files
Encrypted Files
Cynical Instructions
You will also find files scattered around that give pretty detailed instructions on how to deal with this problem.
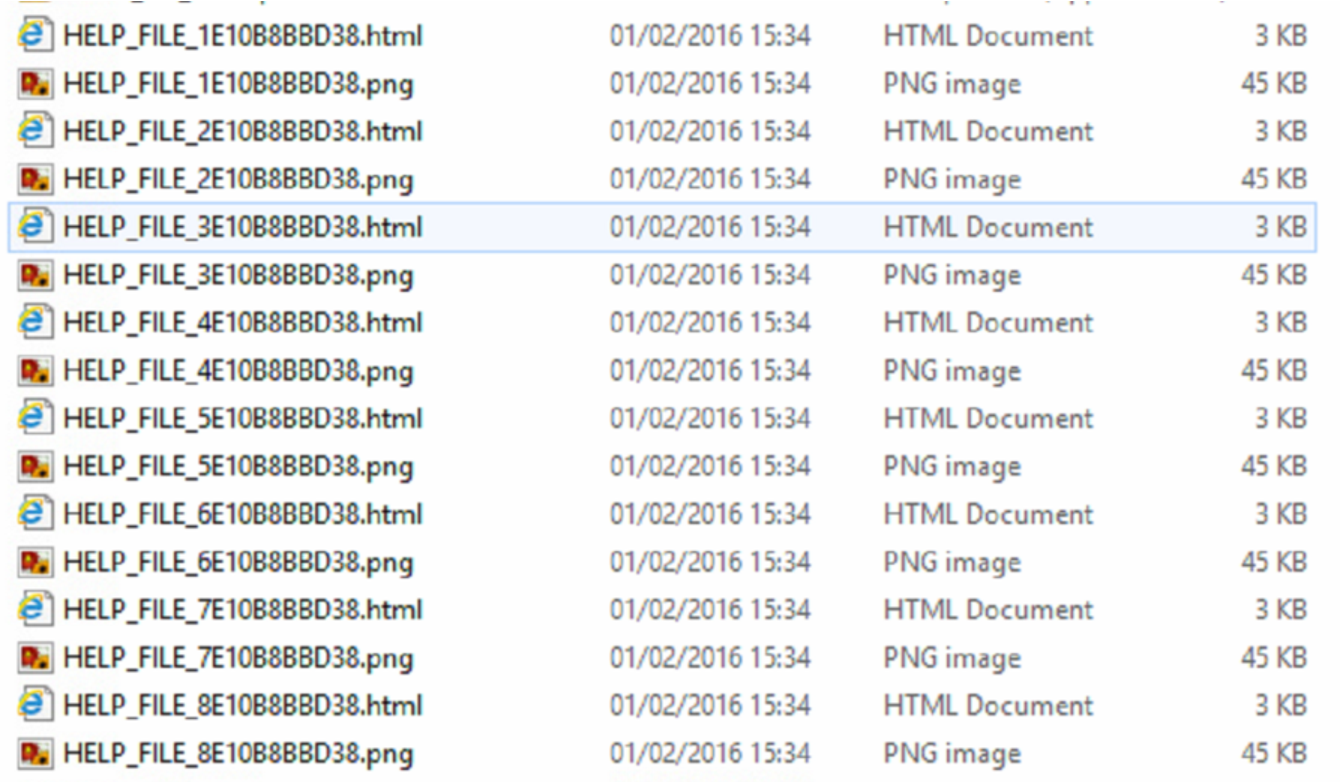 CryptoWall Help Files
CryptoWall Help Files
 CryptoWall instructions
CryptoWall instructions
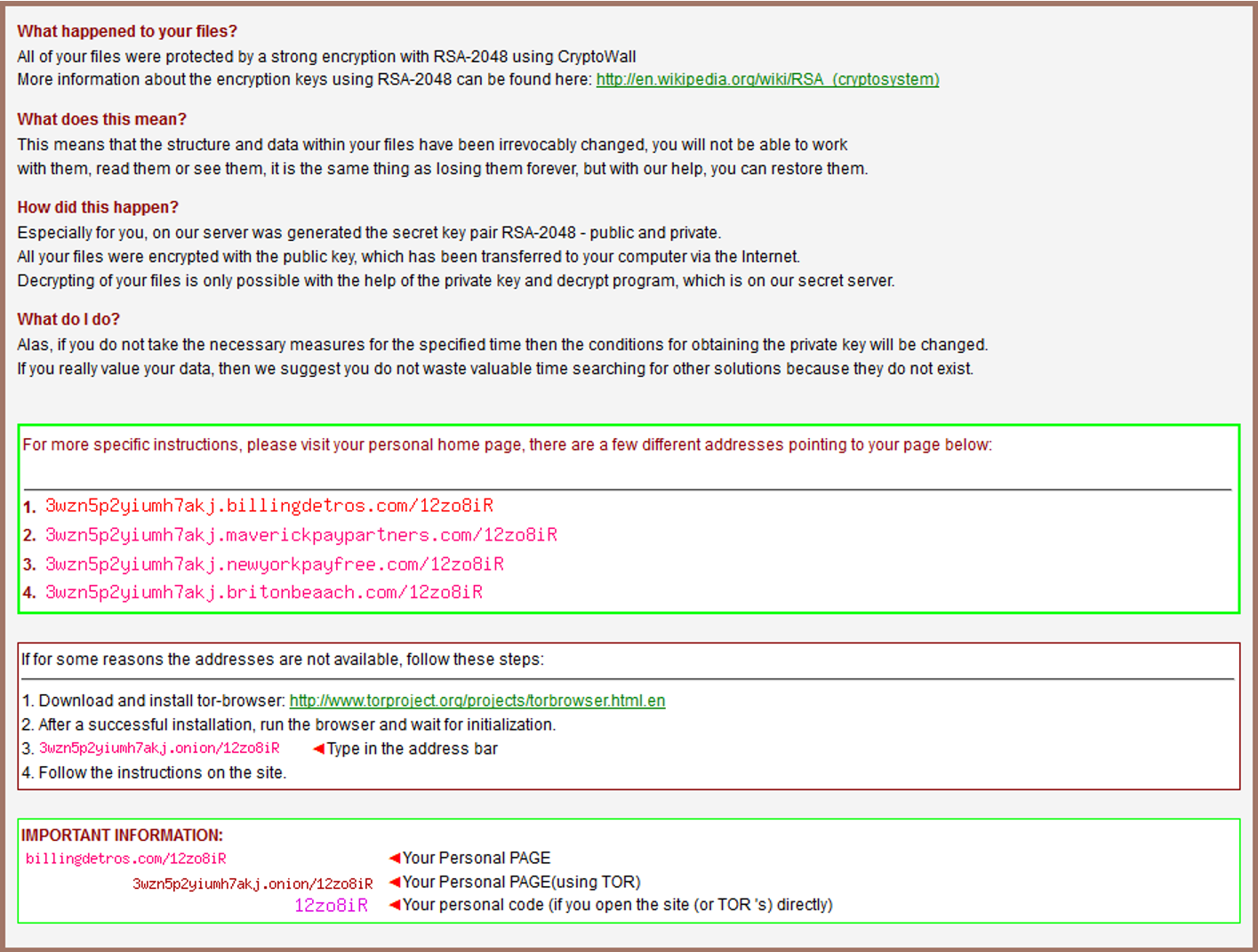
What happened to your files?
All of your files were protected by a strong encryption With RSA-204B using CrypoWall
More information about the encryption keys using RSA-2048.
What does this mean?
This means that the structure and data Within your files have been irrevocably changed, you will not be able to work.
With them, read them or see them, it is the same thing as losing them forever but with our help, can restore them.
How did this happen?
Especially for you, on our server was generated the secret key pair RSA-204B – public and private.
All your files were encrypted With the public key, which has been transferred to your computer Via the Internet .
Decrypting of your files is only possible with the help ofthe private key and decryp program, which is on our secret server.
What do I do?
Alas, if you do not take the necessary measures for the specified time then the conditions for obtaining the private key will be changed.
If you really value your data, then we suggest you do not waste valuable time searching for other solutions because they do not exist.
Decryption – Possible?
Simply put – no, not without taking a risk and paying the ransom. If you don’t have a backup you are faced with a difficult situation.
How to Stop This Happening Again
Traditional Endpoint Protection (Anti-virus) will not protect you from this sort of thing. You need an extra layer stopping your machine(s) from connecting to and unwittingly downloading from malware sites on the Internet. This scam relies on user action in pulling in the external payload and encryption key.
For details on how to protect your outbound connectivity read this page. There is nothing so simple and effective as this product. This must be used as part of a Multi-tiered protection strategy – now an absolute necessity.
Pay or Restore from Backup
There are two options really; restore your files from backup or take a risk and pay the ransom.
Paying the Ransom
There are mixed reports, but paying for previous versions to be decrypted has been fairly successful. The amount being asked for this variant seems higher and there are reports of the keys not being released and therefore the money being lost.
Paying the ransom is a pretty ‘dirty’ business. You will need to follow the instructions that involve downloading the Tor browser and going on the dark web to pay in Bitcoins. You will need to find a method of buying Bitcoin beforehand.
All of this is untraceable and therefore it is unlikely the perpetrators will ever be properly shut down.

